Categories
security
Json Web Token(JWT)
JSON Web Token (JWT) A JSON Web Token (JWT) is an open standard for creating and transmitting information between two parties as a JSON object. Authenticate users and authorize them...
In security, jwt, Nov 23, 2023jwt
Json Web Token(JWT)
JSON Web Token (JWT) A JSON Web Token (JWT) is an open standard for creating and transmitting information between two parties as a JSON object. Authenticate users and authorize them...
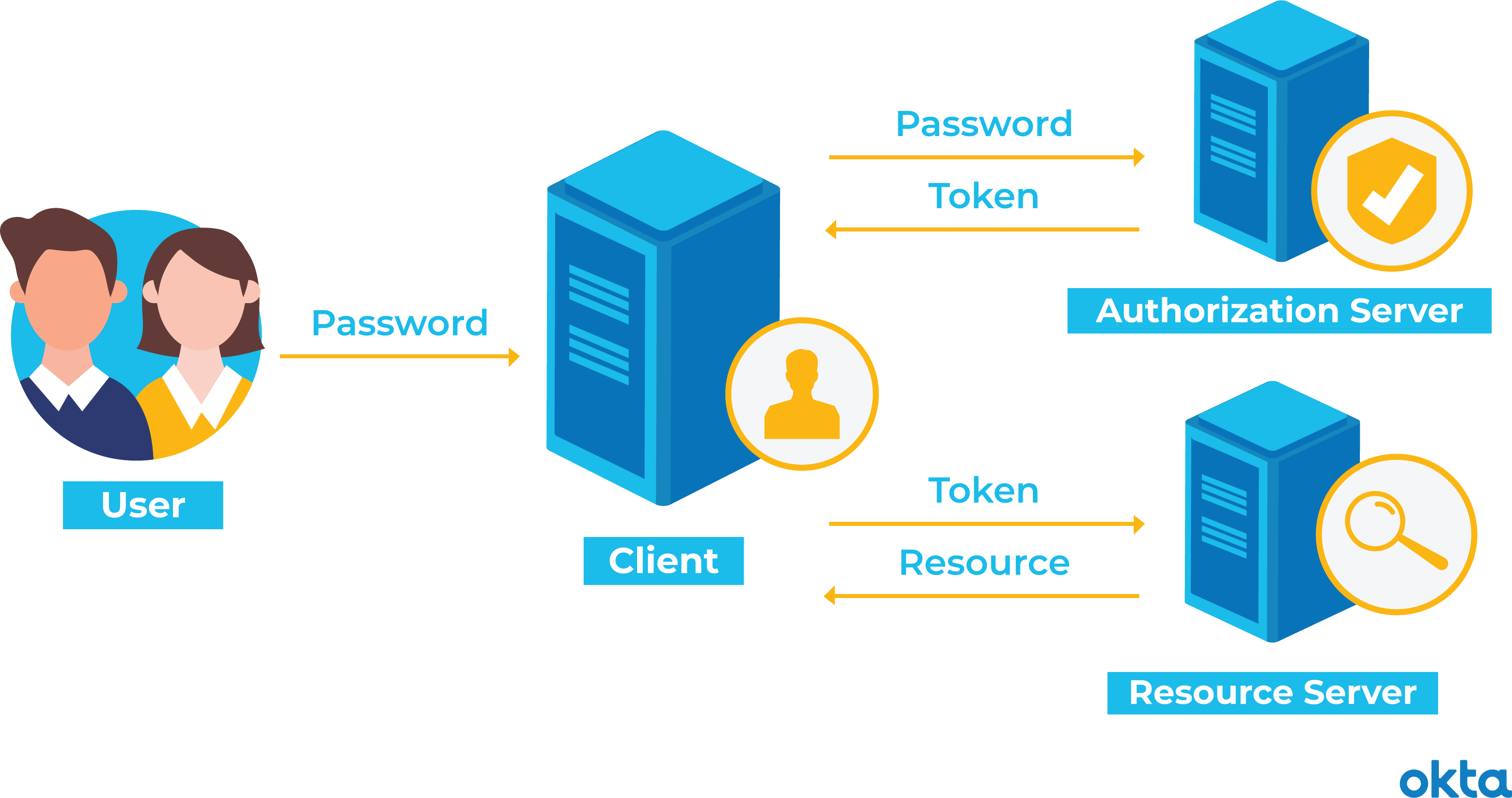
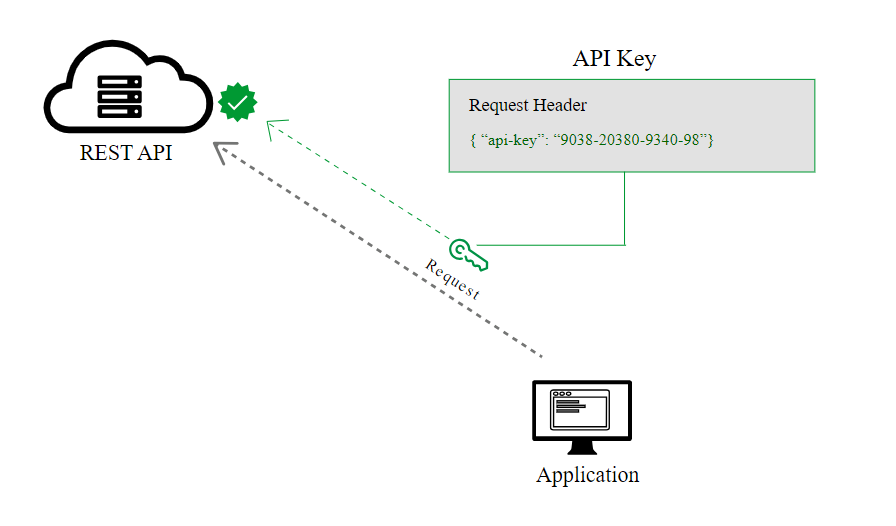
In security, jwt, Nov 23, 2023API Authorization (Types)
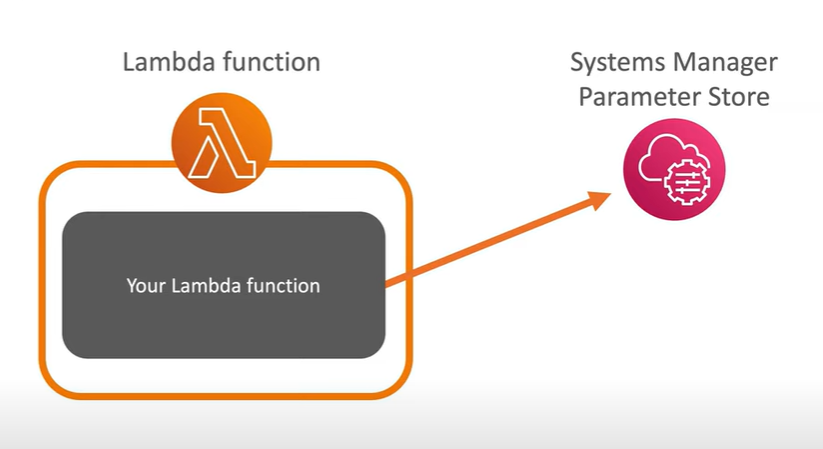
AWS Secrets Lambda Extension to Cache Secrets
AWS Secrets Lambda Extension to Cache Secrets
What is Secret Manager? Aws Secret Manager is a service provided by AWS to store secrets i.e. passwords, credentials, third-party keys, or any such confidential information.
In AWS Secrets Lambda Extension to Cache Secrets, Dec 09, 2023Streaming Protocols
postgis
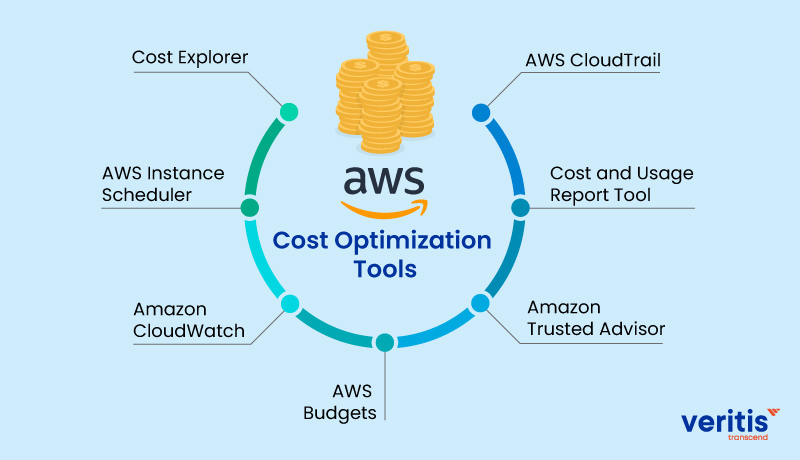
AWS API Gateway Cost Analysis
AWS API Gateway Cost Analysis
AWS API Gateway cost Analysis
In AWS API Gateway Cost Analysis, Dec 16, 2023Geographic Information Systems
LUIGI
Github Commands
Github
Git CommandsGit is a version control system used for tracking changes in computer files. It is generally used for source code management in software development. Git is used to tracki...
In Github Commands, Jan 12, 2024AWS Security
Guildelines of AWS Security Audit(USRetina experience)
Guidelines on AWS security Audit (USRetina experience)
In AWS Security, Feb 17, 2024Training - Phishing
Conference Call Etiquette
Conference Call Etiquette
Conf Call Etiquette DOsPrepare to introduce yourself if it’s your first time - 3-4 statements are good.Log in to the call a min or two before. This gets you the time to chat informal...
In Conference Call Etiquette, May 02, 2024Chatbot with Langchain and AWS Lambda
Serverless ChatBot with Langchain and AWS Lambda
Serverless Chatbots with Langchain and AWS LambdaA serverless chatbot is a chatbot that leverages by the use of serverless computing platforms like AWS ECS or Lambda.
In Chatbot with Langchain and AWS Lambda, May 02, 2024Cloudfront Signed URL
Py-Script
CORS
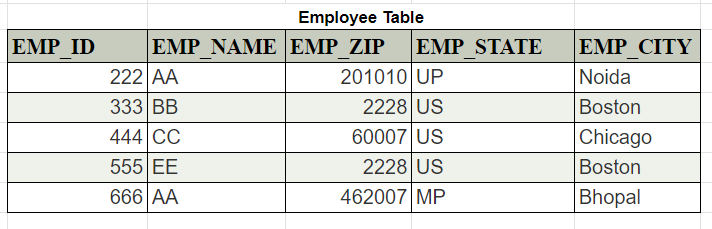
Reference Table
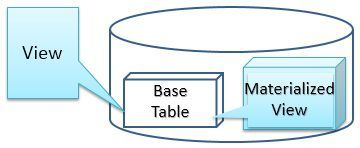
View VS Materialized View
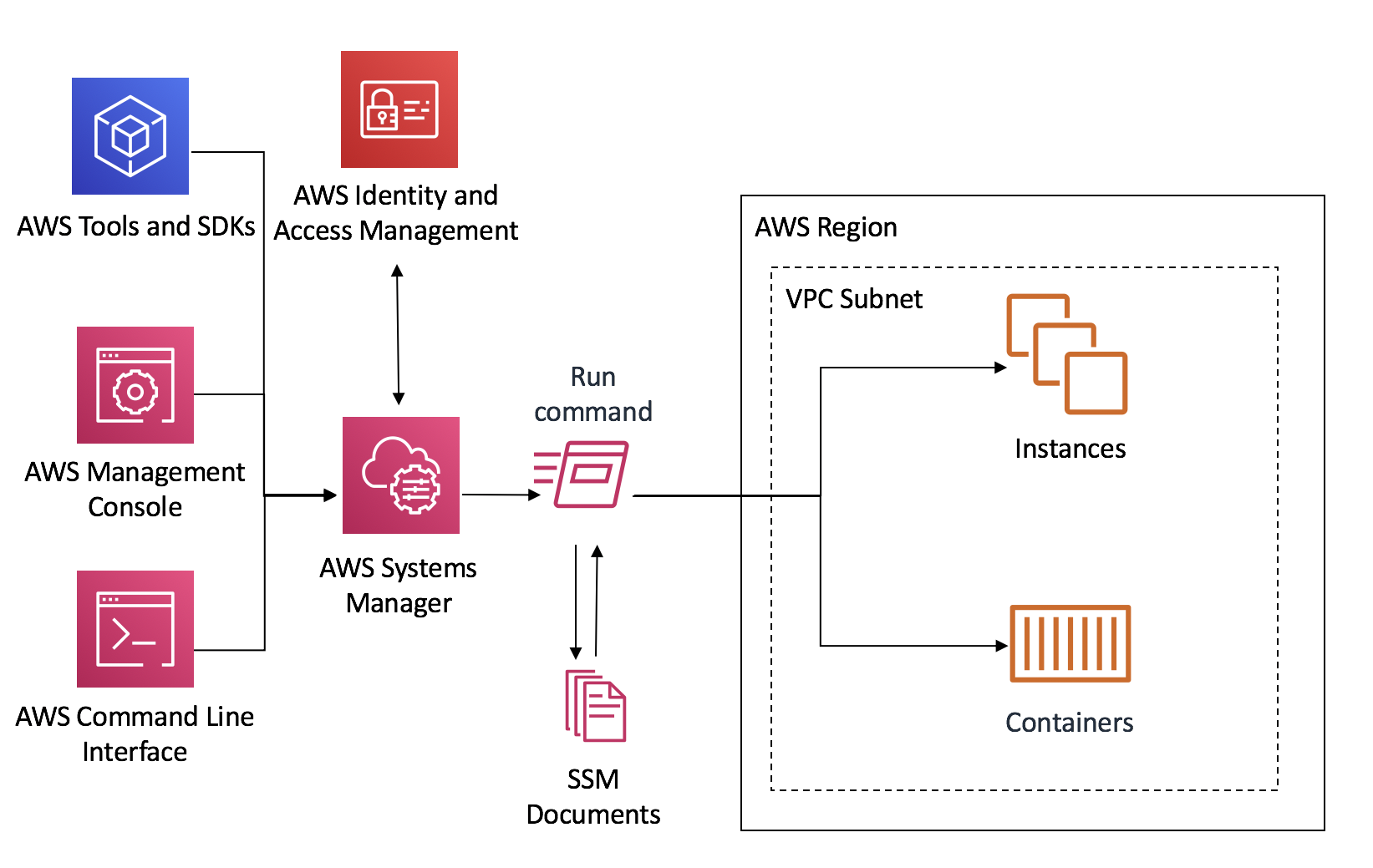
AWS SSM
Mirth Connect
Mirth Connect
Mirth Connect Mirth Connect is a Open Source cross-platform interface engine used in the healthcare industry that enables the management of information using bi-directional sending o...
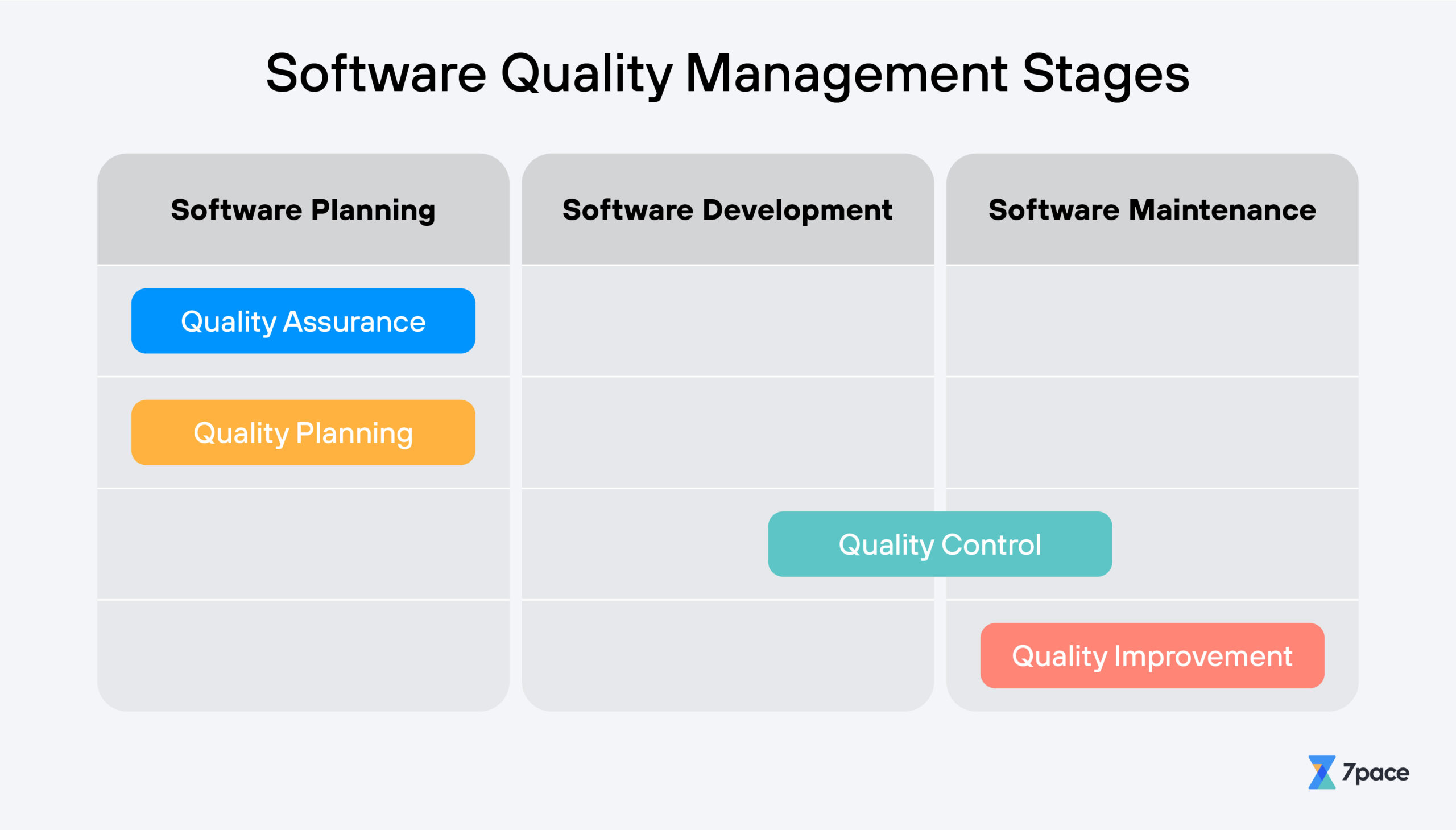
In Mirth Connect, Jun 01, 2024Software Quality Management
Software Quality Management
Software quality - DefinitionIEEE Definitions : The degree to which a system, component, or process meets specified requirements. The degree to which a system, component, or process...
In Software Quality Management, Jun 07, 2024Dimensional Data Modelling
Dimensional Data Modelling
Dimensional-data-modelling-Dimensional data modeling is a design technique used in data warehousing to structure data for easy retrieval and analysis. It is particularly well-suited f...
In Dimensional Data Modelling, Jun 15, 2024UUIDV4 VS UUIDV7
UUIDV4 VS UUIDV7
UUIDv4 Vs UUIDv7Versions of UUID and Their Pros and Cons
In UUIDV4 VS UUIDV7, Jun 15, 2024AWS
Optimal AWS Resources
Choosing optimal AWS resourcesLambda Function URL, VPC Gateways & Endpoint
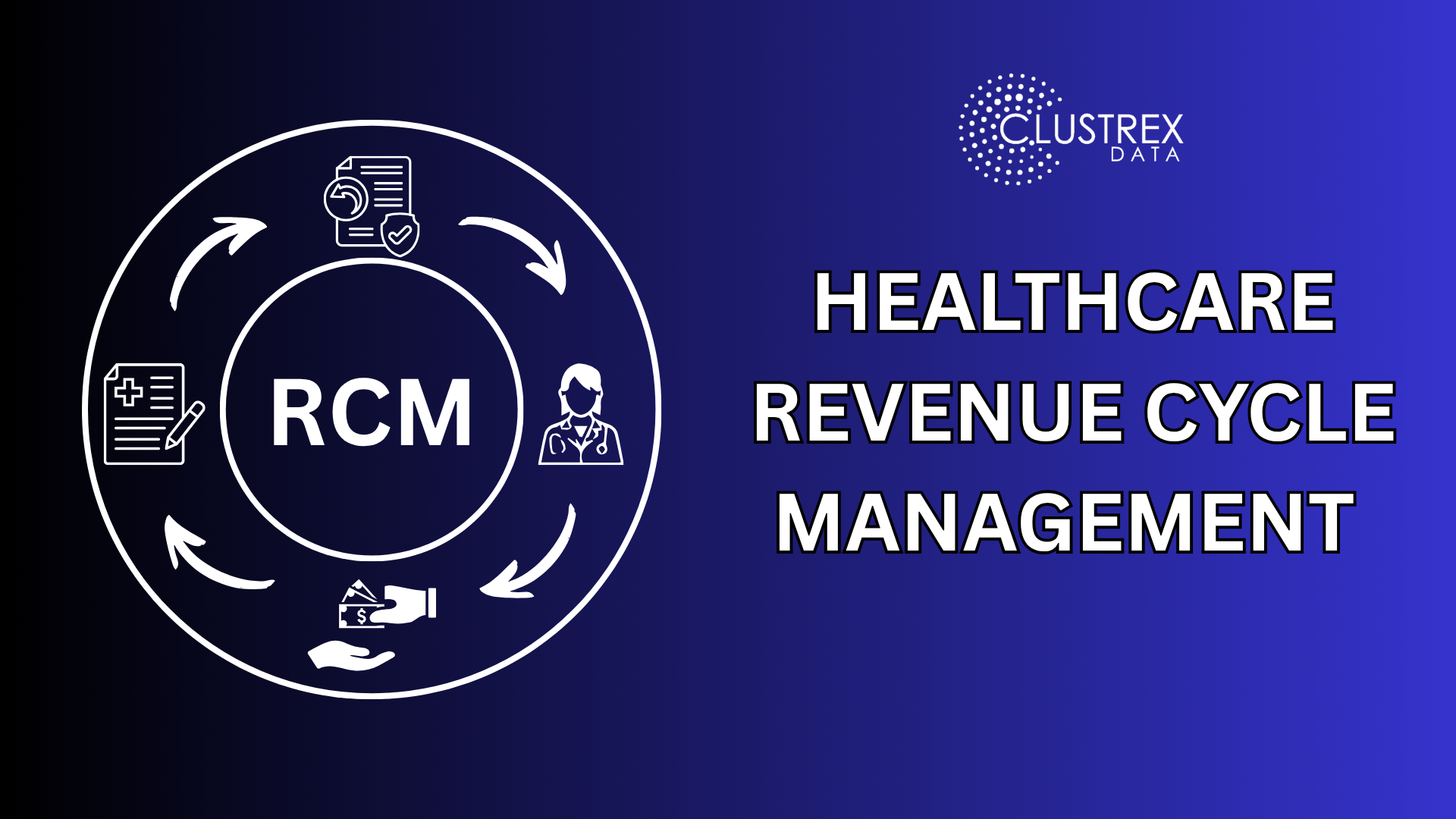
In AWS, Jun 28, 2024RCM
Revenue Cycle Management
Optimizing Revenue Cycle Management (RCM) in Healthcare: A Strategic, Data-Driven Approach
In RCM, Apr 06, 2025Whatsapp Appointment Booking
Appointment Booking Whatsapp
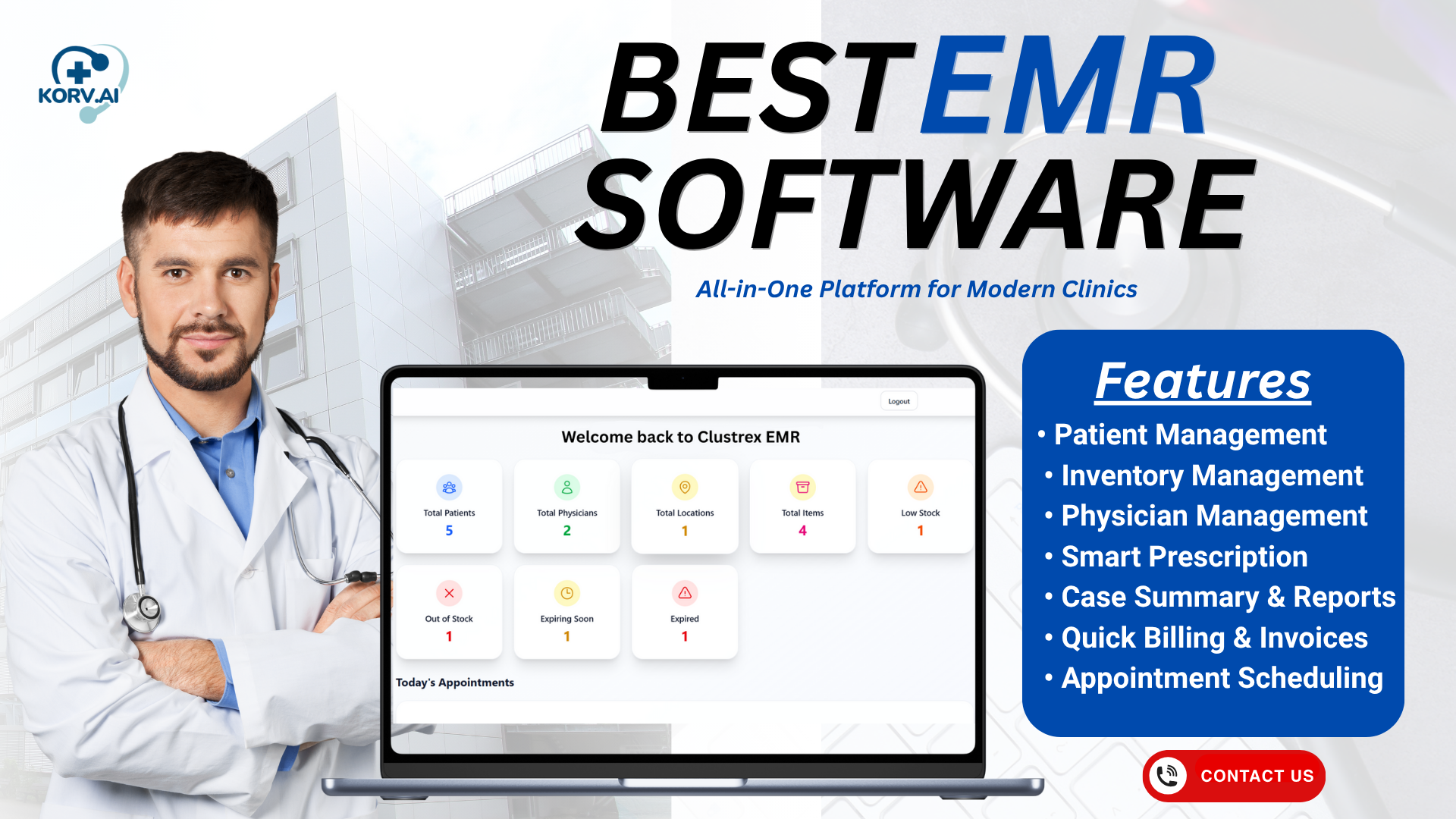
How Korv EMR WhatsApp Appointment Booking Is Transforming Clinic Scheduling in 2025
In Whatsapp Appointment Booking, Nov 14, 2025Celltherapy
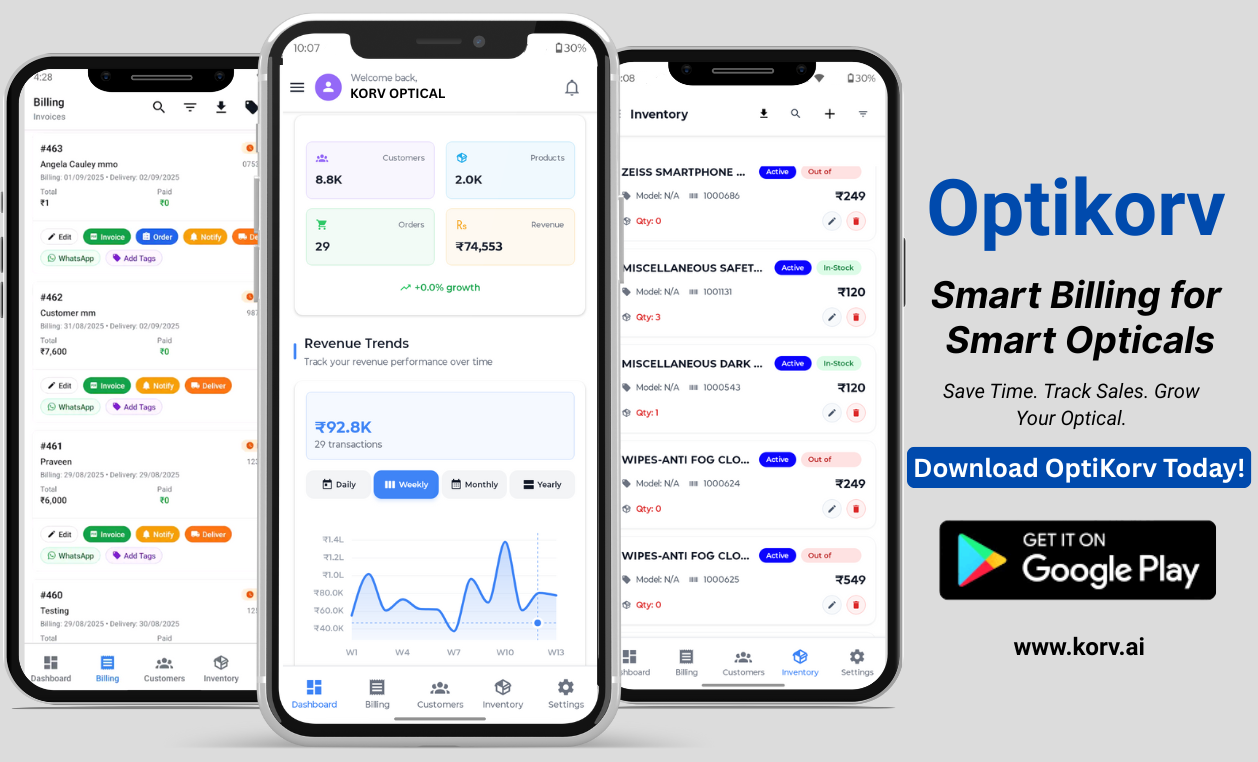
OptiKorv
Object Detection
Real-time Object Detection
Real-Time Object Detection: How Modern AI Vision Powers Smarter Business Operations
In Object Detection, Mar 19, 2026Featured
-
Real-time Object Detection
In Object Detection, -
OptiKorv - The Best Optical Billing App
In OptiKorv, -
Celltherapy
In Celltherapy, -
Appointment Booking Whatsapp
In Whatsapp Appointment Booking, -
Revenue Cycle Management
In RCM, -
Optimal AWS Resources
In AWS, -
UUIDV4 VS UUIDV7
In UUIDV4 VS UUIDV7, -
Dimensional Data Modelling
In Dimensional Data Modelling, -
Software Quality Management
In Software Quality Management, -
Mirth Connect
In Mirth Connect, -
AWS SSM
In AWS SSM, -
View VS Materialized View
In View VS Materialized View, -
Real-time Usecase of Reference Table
In Reference Table, -
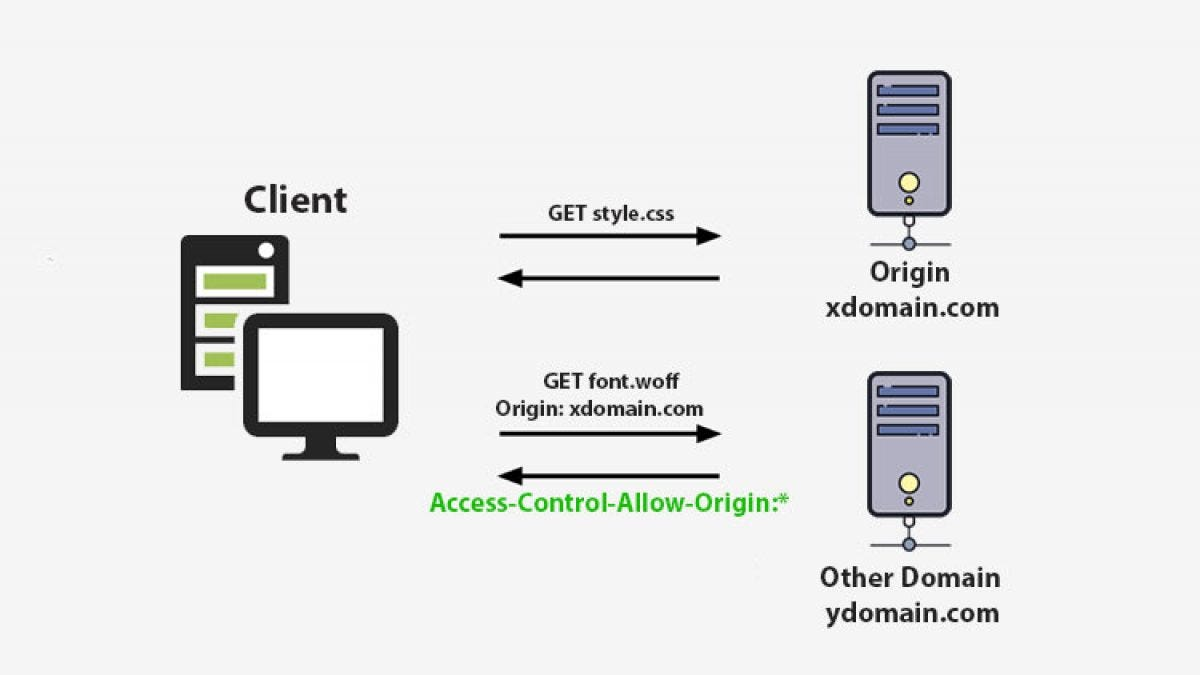
CORS
In CORS, -
Py-Script
In Py-Script, -
Cloudfront Signed URL
In Cloudfront Signed URL, -
Serverless ChatBot with Langchain and AWS Lambda
In Chatbot with Langchain and AWS Lambda, -
Conference Call Etiquette
In Conference Call Etiquette, -
Training - Phishing
In Training - Phishing, -
Guildelines of AWS Security Audit(USRetina experience)
In AWS Security, -
Github
In Github Commands, -
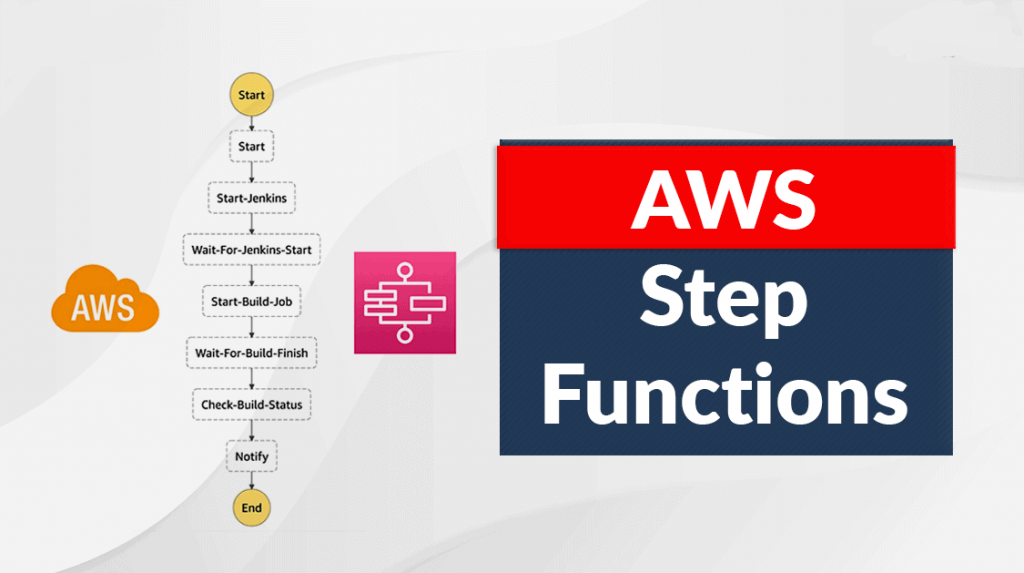
AWS Step Functions
In AWS Security, -
Github
In Github Commands, -
LUIGI
In LUIGI, -
Geopandas
In Geographic Information Systems, -
AWS API Gateway Cost Analysis
In AWS API Gateway Cost Analysis, -
PostGIS
In postgis, -
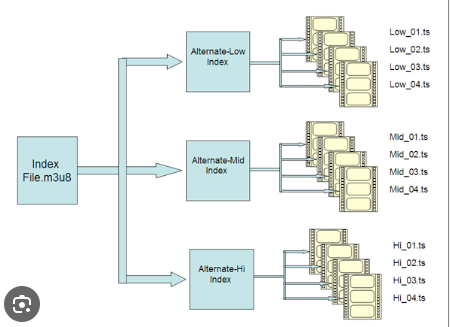
HLS Video Streaming
In Streaming Protocols, -
AWS Secrets Lambda Extension to Cache Secrets
In AWS Secrets Lambda Extension to Cache Secrets, -
API Authorization (Types)
In API Authorization (Types), -
Json Web Token(JWT)
In security, jwt, -
Access and Refresh Tokens
In security, jwt, -
Tableau JavaScript API
In security, jwt,