Social Engineering
- Social engineering is a tactic used in cyber attacks that relies on human interaction and psychological manipulation to trick individuals into making security mistakes or giving away sensitive information. Unlike traditional hacking that focuses on exploiting software and hardware vulnerabilities, social engineering exploits human vulnerabilities by deceiving people into breaking normal security procedures.
What is Phishing ?
- Phishing is a type of cyber attack that involves deceiving individuals into revealing sensitive information, such as usernames, passwords, credit card numbers, or other personal details. The attackers typically masquerade as a trustworthy entity in digital communications, aiming to trick the victim into making security mistakes or giving away information voluntarily.
Phishing Types & How it works
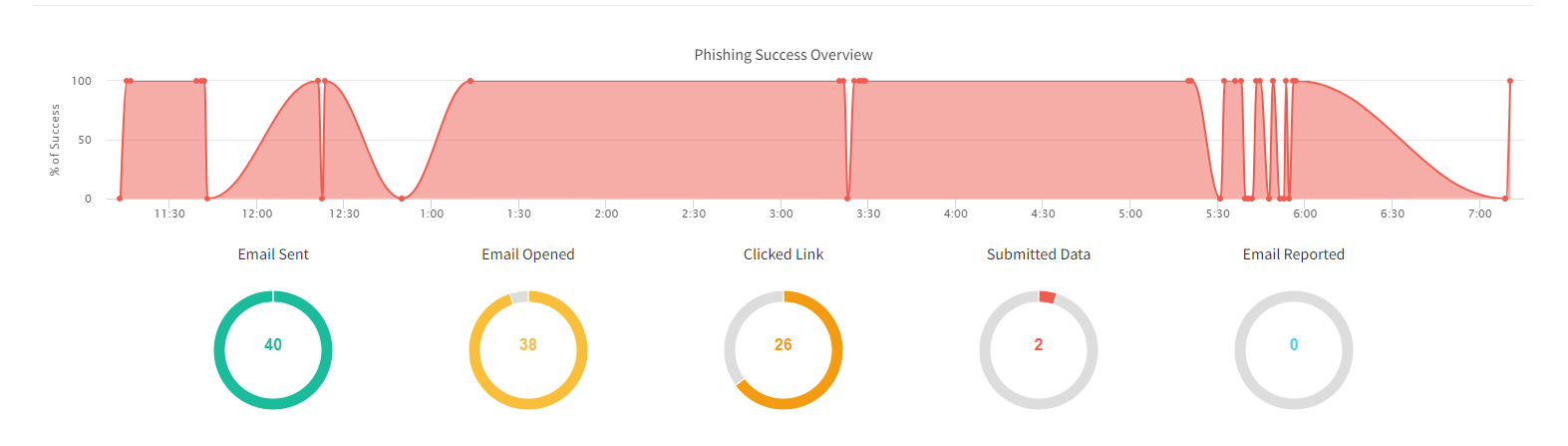
- Email Phishing: This is the most common form. The attacker sends an email that appears to be from a legitimate source, such as a bank, a credit card company, or a well-known corporation. The email may urge the recipient to act quickly, invoking a sense of urgency or fear. It often contains a link that leads to a fake website that closely resembles the real one, where victims are prompted to enter personal information.
- Spear Phishing: Unlike the broad targeting typical in phishing, spear phishing targets specific individuals or companies. These attacks are personalized to increase their effectiveness, with the attacker gathering personal information about the victim beforehand to create a plausible scenario.
- Smishing and Vishing: These are variations where phishing attempts are made via SMS (smishing) or voice calls (vishing). In smishing, text messages can lure victims to malicious sites or prompt them to divulge personal info. In vishing, the attacker usually pretends to call from a reputable organization to trick victims into sharing private data.
- Whaling: This type of attack targets high-profile individuals like C-level executives or administrators, often involving crafted emails that address high-level business matters, which can result in significant data breaches or large financial losses.
Common Characteristics of Phishing Attacks
- Urgency: Phishing messages often convey a sense of urgency, pressuring the recipient to act quickly.
- Too Good To Be True Offers: Enticing offers that seem too good to be true are often bait to attract victims.
- Hyperlinks: A common tactic is the inclusion of a malicious link that redirects the user to a fake website.
- Attachments: Emails may include attachments that contain malware or ransomware, which infect the user’s system upon opening.
- Spoofing: The email address or website address may look extremely close to the legitimate one, with only minor differences that can be easily overlooked. Eg facebok.com or youtub.com
Prevention Tips
- Be skeptical of unsolicited messages that ask for personal information or direct you to websites where personal details are required.
- Double check before entering your username and password for any account - if you are asked to change your password and taken to some other user interface / site / hyperlink
- Verify the authenticity of requests for sensitive information by contacting your manager directly through official channels.
- Use updated antivirus software and email filters to help catch and block phishing attempts.
- Educate yourself and others about the tactics used in phishing attacks and promote awareness within organizations.
- Secure Anti-phishing browser extensions – cloudphish ?
- Browse internet with care, be alert about malicious attempts
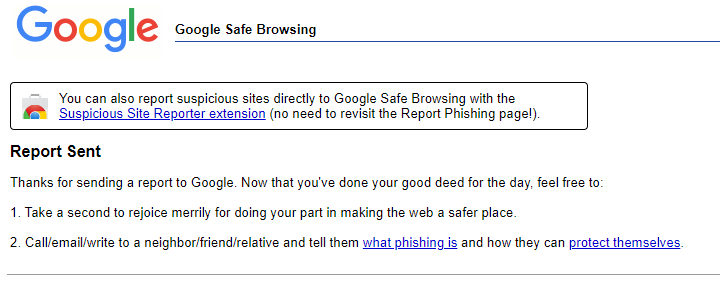
Phishing Test conducted on 16th May 2024
What can be better?
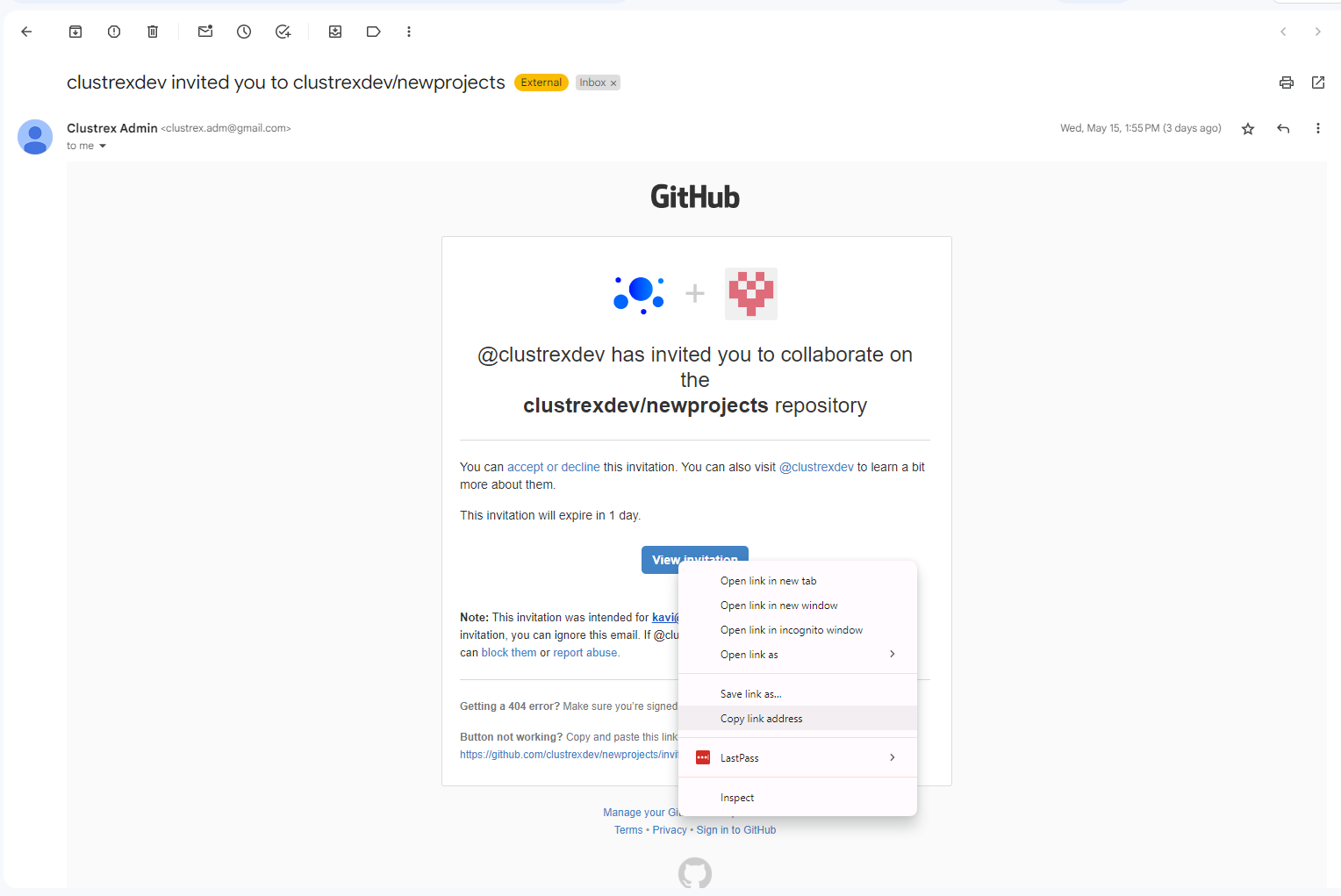
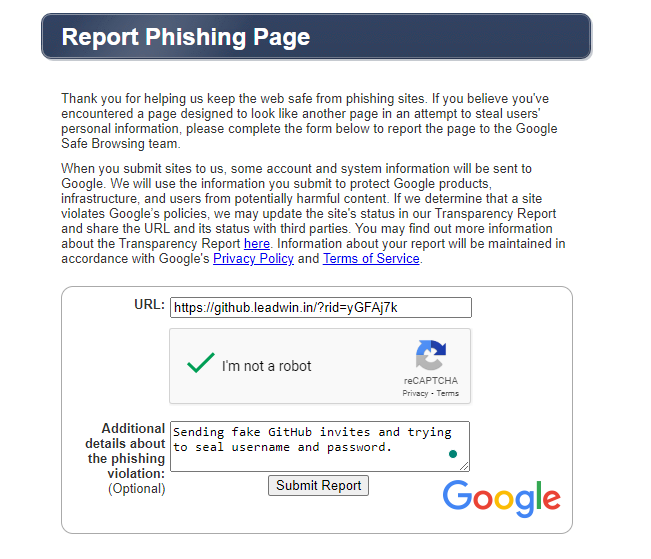
Google Report Phishing Website